TLDR
This guide provides everything you need to know to protect your crypto from hacks. Protecting your digital assets from theft and hacking is paramount in cryptocurrency. The high level of the market’s perplexity and the system’s nature make it even more challenging. Security risks include digital theft, data breaches, and losing your private keys or seed phrase.
The best ways to protect yourself include some of the following:
- Using a hardware wallet, setting up two-factor authentication.
- Creating a strong password.
- Avoiding fake websites.
- Not entering your seed words on a website.
- Use a different password for your wallet.
- Being wary of emailed files.
- Finally, offline hardware wallets are the safest way to hold crypto.
Protecting Your Crypto Assets from Hacks and Threats
As the crypto market continues to grow, it has become increasingly important to understand the risks associated with cryptocurrency trading. One of the most common risks is hacking. This can lead to the loss of funds and the disruption of services in the crypto investment world.

This article discusses protecting your crypto assets from hacks and other threats. We will look at the best security practices for crypto users. These include using a hardware wallet, setting up two-factor authentication, etc.
The Main Security Risks of Crypto
The significant risks that anyone holding cryptocurrency should be aware of are:
Getting Scammed
Crypto hackers will try to trick you into giving them your private key by sending you an e-mail designed to look real. Sometimes, they pretend to be associated with a fake website that looks legitimate to gain access and steal cryptocurrency.
They sometimes also pretend to be a real crypto trading platform. If someone is trying to steal your private key for cryptocurrency transactions, they will often try to get you to reveal it. This can happen during a conversation on Skype, over the phone, or through SMS text messaging.

Keeping your Crypto Funds on Centralized Exchanges
One of the most significant risks of holding crypto on centralized exchange is leaving your digital coins and assets vulnerable and susceptible to hackers. If you own crypto on a sale, you should keep it sparingly and try to withdraw often into your crypto wallet.
Losing Your Private Keys or Seed Phrase
This is the same as losing a wallet full of cash. If you lose your private key or seed phrase, you lose access to all the currency in your wallets. It’s gone forever.
Malware
Hackers are always trying to find new ways to infect your computer with malware or keyloggers, viruses that capture your keystrokes and can steal your private keys. The most common places you see malware or keyloggers are in fake emails, on fake websites, on third-party services, and on remote access tools like LogMeIn.
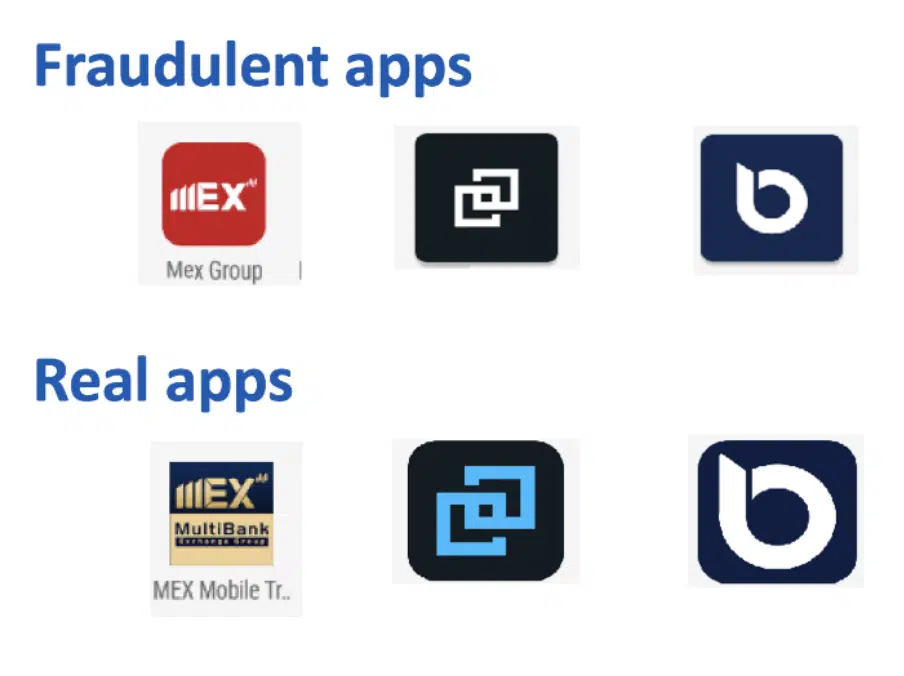
Fake Apps or Spoofing
The best way to protect yourself from fake version apps is to always download from verified sources and the official app store. Another great way to check if a site is fake is by using validator services like HTTPS Everywhere or Chrome’s built-in security checker. Check your download history if you need help remembering where you got an app.
Protocol Hacks
This is often called a 51% attack when someone gets over half the hash power from their network. It can be done by owning more than half of the mining equipment, buying up a lot of mining hardware, or hacking a large enough percentage of the network to get 51% control over how much digital money or currency is created.
How to Protect Your Crypto from Hacks
The easiest way to protect a crypto account from all these risks is by:
Withdraw Your Crypto
Most exchanges offer “hot wallets, “ meaning you can withdraw funds from your crypto wallet directly into a bank account through a wire transfer or by tapping into USD funds right after the transaction.
Some exchanges allow you to trade cryptocurrencies against fiat money like the US dollar or local currency through your crypto wallets and then withdraw those funds directly from your crypto exchange account.
Backup Your Seed Words Properly
Remember that if you lose your private key or seed phrase, you lose access to all the currency in all your wallets. This is just as important as keeping your private keys safe.
Use a Strong Password
Most people put a password on their computer but use something straightforward to remember. As with all security measures, if you don’t use a strong password on your computer, you won’t get any benefit from it. Never use your real name, e-mail address, or personally identifiable information using an online wallet. Change the password frequently and never avoid reusing the same password to keep your crypto safe. You can create passwords using a password manager.
Use Two-Factor Authentication for Your Exchange

Many of the largest crypto exchanges, crypto industry, and sites now use (2FA) — to avoid crypto scams and theft. You’ll need to enter a second code before accessing your account.
Some even send the code via text messages SMS, while others have apps where you can manually join it. Check your cryptocurrency exchanges to see if they offer 2FA and how to set it up on your device.
Use a Different Password for Your Wallet
Creating a new wallet will automatically generate a seed phrase attached to your wallet address, also known as a private key, that you must use to log in. If you lose it or your device gets stolen, the hacker will be able to get access to all of your cryptocurrency.
Use a Hardware Wallet If Possible
Hardware wallets have become the primary method of protecting cryptocurrency. You can keep physical devices in your pocket or on your keychain. They use an encrypted chip, usually NFC or Bluetooth enabled, to access and communicate with devices easily. Cold wallets and hot wallets are also great ideas. However, it has been said that cold wallets are considered to be less risky.
More details
The Ledger Nano X is a must-have, secure hardware wallet for cryptocurrency. It features easy mobile pairing, a sleek design, Bluetooth support, and robust security features like a safe chip and two-factor authentication.
-
Supports 5500 various cryptocurrencies.
-
Private keys are encrypted.
-
Desktop and mobile devices are supported.
-
Bluetooth enabled.
-
Allow 100 apps storage.
-
Fairly overpriced against the competition.
-
Only 100 apps are allowed.
-
Bluetooth works solely with mobile.
More details
Ledger Nano S Plus is a fortress-like protection for your digital wealth, sporting an affordable price point. This crypto wallet supports many cryptocurrencies and blockchain networks, making them easily managed via the reputable Ledger Live app. Despite its significant advantages, some users have noted the lack of storage capacity.
-
Support for up to 5,500 cryptocurrencies.
-
Private keys are always offline.
-
Integration with other hot wallets.
-
Support for staking.
-
NFT support.
-
High fees for Ledger Live crypto purchases.
-
Limited app space.
-
Small display.


More details
The Trezor Model T is a high-quality hardware wallet that offers top-notch security for cryptocurrency investors. Trezor is known for its transparency and trustworthiness. The ability to store 1500+ tokens and Non-Fungible Tokens (NFTs) justifies the premium price of $219. However, some users have reported issues with the MicroSD card slot. Trezor Model T is a solid pick to safeguard crypto despite minor concerns.
-
It supports 1400+ crypto assets.
-
Touch screen for a user-friendly operation.
-
It supports NFTs storage.
-
Too expensive when compared to its competitors.
-
It has limited mobile compatibility.
-
A bulky design that is quite hard to carry around.
Check the URL (Avoid Fake Websites)
If you’re downloading a cryptocurrency wallet or making crypto transactions from their website or an app store, always check the URL. The safest way to do this is to verify every time you log in that you are on the correct domain and are being served by the same certificate and be careful of malicious links.

Don’t Enter Your Seed Words on a Website
If you get an e-mail with a link to a website that looks like it’s from a cryptocurrency exchange, never click on it. Instead, add the URL to your browser’s “fraudulent sites” list and contact the site administrators through a customer service e-mail address. If they respond within 48 hours, report them to their hosting companies and web admins.
Avoid Public Wi-Fi
Never connect to a public Wi-Fi network to keep your cryptocurrency and digital investments safe. Most are known for being vulnerable and hacker-friendly, and even if you don’t get hacked, just being connected to them can reveal your IP address and bank account info.
Subscribe to a VPN Service
A lot of these warnings apply to regular internet use as well. However, virtual private network service will block your IP address from the websites you are trying to visit, protect your online wallets and online transactions from other people logging in over your connection, and provide an adequate and secure internet connection. Check out our updated list of the best VPNs for crypto trading.
Be Wary of Emailed Files
If you receive an e-mail with a file that’s supposed to be a digital wallet or private key, don’t open it. File attachments are one of the easiest ways to infect a computer with malware and steal crypto because they give bad guys access to your machine by tricking you into opening them.
This is a common misconception that you can actually 'hack' the blockchain. The blockchain is entirely decentralized and cannot be hacked in any way.
Cryptocurrencies are protected by "hashes," 256-bit long data strings that act like your crypto's digital fingerprint.
The best ways to protect your cryptocurrency wallets are to keep your private keys safe and use a secure wallet and exchange partner.
The safest way to hold your crypto is by using offline hardware wallets.












